That's ridiculous.
At some point business owners need to begin holding accountable the vendors who provide inadequate security products, software developers and firms that release buggy, vulnerable operating systems, browsers, and applications, and users who don't follow safe computing and web browsing guidelines. And they need to demand more robust authentication and authorization mechanisms from their financial institutions.
It's absurd that money movement practices have not evolved in the face of increased threats and hundreds of successful exploits. From Wired:
The FBI says thieves have stolen about $40 million in this way in more than than 200 cases they’ve investigated in the last two years involving small to mid-size companies and organizations. Such companies generally do not employ dedicated computer security staff or have extensive knowledge about how to protect themselves with firewalls, anti-virus and other measures and policies.
It's a common attack strategy - aim for the weakest point in the system. Why attack a bank directly when the soft underbelly of naive business owners and employees remains exposed, ripe for the picking?
Small businesses need to come to terms with the fact that computer security is a mandatory cost of doing business. It isn't 1982 anymore. You can't ignore information security any more than you can keep a manual ledger or crank out your financials on an adding machine.
So let's say you take the advice of the FBI and ABA and set up a dedicated computer within your network for online banking only. Guess what? You're still connected to the internet, and you're still not 100% safe.
I can redirect your access to your online banking site via DNS cache poisoning. I can compromise another computer (that's not dedicated) within your network and use it to infect and take control of your dedicated PC.
I'm able to conduct IP address spoofs, or perform a man-in-the-middle attack to snag the traffic going between you and your financial institution.
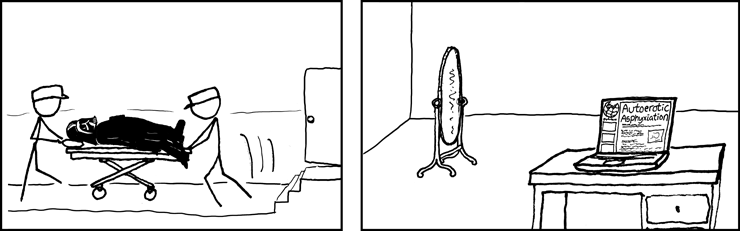
If these don't work, there's always session hijacking, or replay attacks, or compromising weak encryption keys. And a dedicated PC doesn't prevent attacks via social engineering.
Here's a couple of things every small business should consider:
- Use a non-Microsoft platform for conducting online banking transactions. Since Windows and Internet Explorer continue to have a dominant market share, they attract the most attention from attackers.
- Don't use wireless for online banking. It's too difficult to secure for those without the correct technical expertise.
- Use Mozilla Firefox, Opera, or some other browser.
- Install good antivirus software and keep it updated.
- Use a tool like Secunia CSI to make you aware of vulnerabilities and end-of-life software installed on your systems